Cybersecurity must be at the forefront of all of your development projects because security risks are everywhere in today’s world. Whether it is an individual, any company, or the government, security has become a major concern for everyone. So, it is essential to ensure the best security practices for secure software development.
The latest reports claim that cybercrime is estimated to cost companies $10.5 trillion by 2025. These are staggering numbers, underscoring the critical need for secure software development!
In this blog post, we will deeply delve into software development security and uncover the best security practices you need to ensure software development. Let’s start reading!
Understanding Secure Software Development Policy
A secure software development policy is an established set of guidelines, procedures, and standards that guide how you should design, develop, and maintain software to ensure the highest levels of security throughout the development lifecycle.
The goal of this software development policy is to make a final product as secure as possible. It aims to find out and mitigate any potential security threats and vulnerabilities during the software development process.
What is the Secure Software Development Lifecycle (SSDLC)?
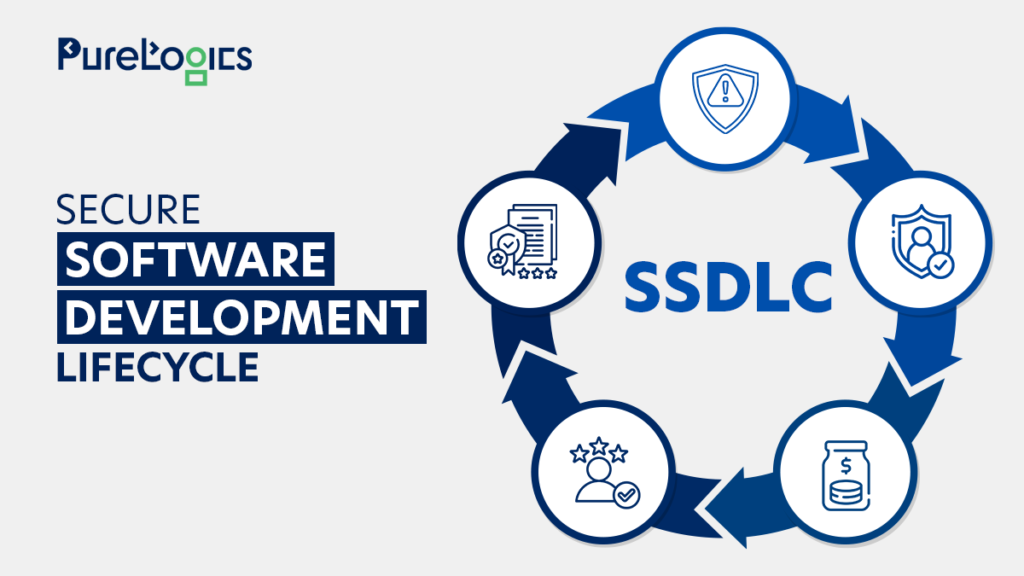
Secure Software Development Lifecycle (SSDLC) is a ready-made solution that offers a structured approach to software development. SSDLC places security as the first and foremost priority.
It is a comprehensive set framework for strengthening security and compliance in all stages of software development, from concept to deployment and maintenance.
Top 5 Benefits of Secure Software Development Lifecycle
The benefits of secure software development are considerably significant and worth mentioning. Look at the following benefits, and make sure that you always ensure robust security measures in the development process.
Risk mitigation: SSDLC identifies and addresses security threats and vulnerabilities throughout development.
It not only reduces the probability of cyberattacks and security breaches but also increases the overall productivity of the development process.
Ensures user privacy: Secure software development ensures that the data and information of your users remain fully secure.
Cost savings: No one loves dealing with the aftermath of a security breach. Thanks to the secure software development cycle, it helps companies save their hard-earned money by preventing security concerns on time.
Enhanced reputation: Secure software instills trust in customers and enhances the brand image of an organization.
Ensures compliance: Security regulations like HIPAA, GDPR, Drummond Certification, etc., require companies to strictly follow security measures.
What Happens If Software Development isn’t Secure
Failing to perform secure software development can lead to loopholes that threaten the security of your company, compromise its sensitive data, grant privileges to people who can abuse these things, and more.
Here are some of the dire consequences of insecure software development
Data breaches: Software that is unsecured is like an open invitation to cybercriminals. They can steal the sensitive data of your intellectual property and dedicated users.
Reputation damage: Insecure software can destroy the hard-earned reputation of your company and lead to a loss of customer trust.
Legal consequences: Insecure software development can lead to serious legal actions and hefty regulatory penalties. So, companies should strictly follow industry-related security compliance standards.
Financial loss: No one loves addressing the aftermaths of a security breach. Thanks to SSDLC, it helps companies save their hard-earned post-development costs.
Downtime and disruption: Moreover, insecure software can lead to system downtime. It will not only impact the productivity of business but also cause serious financial losses.
Why Do Developers Skip Security Steps
74% of companies release software (frequently or routinely) with unaddressed vulnerabilities, internationally recognized reports, and claims.
But why does it happen? Following are seven reasons that you must know as a business leader. This list of reasons will help you develop safe and secure software for your company.
- Lack of example from top management. Many developers don’t think these steps are necessary.
- They assume that the security of web applications isn’t their problem.
- Developers have less time and resources, which leads to the development of insecure web applications.
- Many businesses think that anything that is related to “security” isn’t a part of their domain. They assume that security must be handled by a dedicated security team.
- Many software developers have insufficient knowledge of web application security.
- Many developers struggle to fix the security mistakes of other developers.
- Frustration issues due to bad tooling are another great reason for insecure software development.
10 Best Security Practices for Secure Software Development

Now that you understand how important it is to perform secure software development and what are the serious consequences of neglecting it. Let’s explore the top 10 best security practices you must know for your software development projects.
Comprehensive Requirements Analysis
Start with a comprehensive analysis of security requirements. You must identify potential security threats and vulnerabilities related to your software development project. This step is the most important to build a secure foundation.
Secure Coding Practices
You must train your software engineers in secure coding practices. Encourage them to use secure coding guidelines, tools, and best practices to minimize the chances of security threats and vulnerabilities during coding. You may also hire credible third-party developers for this task.
Regular Code Reviews
Implement regular code reviews and leave no stone unturned to identify and sort out security issues. You may ask for peer reviews, as they can catch vulnerabilities that you may have missed during development.
Testing and Quality Assurance
Integration of security testing into your QA process is a great way to ensure safe software development. Perform intensive and strict security assessments to identify and resolve security issues. The assessments include penetration testing and threat scanning.
Authentication and Authorization
Implement the strictest and latest authentication and authorization mechanisms. It will ensure that only authorized users get access to your company’s sensitive data and functionality.
Data Encryption
Use encryption to protect your data (both in transit and at rest). The encryption process will protect sensitive information from unauthorized access.
Patch Management
You need to stay vigilant about applying security patches and updates as soon as possible. If your software is outdated, it is like an open invitation to security attacks and breaches.
Security Awareness Training
Another important step in secure software development is investing in ongoing security awareness training for your development team. Make sure that all your team members understand why it is important to consider security measures.
Incident Response Plan
Develop a well-educated and well-defined incident response plan. Your response plan should handle all types of security breaches effectively. Always be prepared and proactive to minimize the potential impacts of a breach and decrease downtime.
Third-Party Security Assessment
Last but not least, if your software or web application relies on third-party components or libraries, make sure to completely assess their security parameters. Any sort of vulnerability in third-party code can lead to security breaches and cyber threats.
Make sure to incorporate all aforementioned security parameters into your software development process if you want to enhance the overall productivity and resilience of your software against cyberattacks.
Final Words You Can’t Skip
When it comes to protecting the assets of your company, there is no silver bullet. However, by maintaining these essentials, you will be able to make your business a much more challenging target.
These above-mentioned top ten software security measures will assist you in ensuring software security.
We at PureLogics develop software by following international standards of security. Our clients trust us because we never compromise on security and compliance.
Contact us now, and let’s build secure web applications.
PureLogics: We believe in logic, not magic!


 [tta_listen_btn]
[tta_listen_btn]
 November 6 2023
November 6 2023