Dr. John receives a panicked call at 2 a.m. about patient medical records that have just been leaked online by hackers. As he stares at his laptop, he realizes that every patient file is at risk, and he has 48 hours to figure out what to do. He wishes he had a system where it was impossible to read a patient’s record. This is where end-to-end encryption in healthcare applications comes in.
We must all recognize that the development of secure healthcare mobile apps is not a luxury but a necessity, as rising cybersecurity threats are resulting in significant financial and operational losses. Now, attackers can relentlessly exploit any weaknesses in the security controls. All in all, healthcare systems face two major threats:
- Widespread attacks on cloud backups, logs, and archives.
- Session-based attacks that exploit weak authentication.
If you are in any way thinking it’s just that, then remember to consider any weaknesses or gaps in security controls within healthcare apps. For instance, the use of outdated technologies or a lack of security expertise can be a loophole that cybercriminals can exploit. Moreover, the healthcare sector faced more cyber threats in 2024 compared to any other industry.

Indeed, it is essential to address these challenges with a proactive approach, taking measures such as robust encryption, multi-factor authentication, and continuous monitoring. Additionally, let us explain why cybercriminals often target healthcare applications.
Why Are Healthcare Applications at High Risk?
Data privacy in the healthcare sector is of utmost importance because any breach can directly affect a patient’s trust and safety, and also expose healthcare facilities to legal accountability. Some of the top reasons why healthcare applications are highly vulnerable are given below:
- Contain Patient Healthcare Information: These apps store Protected Health Information (PHI), including medical records, diagnoses, prescriptions, and insurance details, making them a high-value target for cybercriminals.
- Data Transfer: In healthcare, data is constantly in motion, whether it involves patient monitoring or remote telehealth sessions. Moreover, improper data encryption can lead to a risk of interception, making end-to-end encryption in telemedicine apps necessary.
- High Black Market Value: The stolen health records are worth more due to the presence of sensitive patient data. Recently, the UnitedHealth Group CEO stated that they had to pay $22 million in ransom.
- Lack of Security Awareness: Many healthcare facilities lack dedicated security teams or funding, leaving them prone to cyber attacks. The best strategy here is to hire a healthcare software development company, as they follow security protocols at every step of the process. Additionally, ensure to include measures like encryption, two-factor authentication, etc.
- Complex Infrastructure: Most healthcare providers overlook this, but third-party systems (labs, pharmacies, and insurers) introduce additional attack surfaces and potential vulnerabilities.
- Legacy Systems: Many healthcare systems still rely on legacy systems, which often lack essential security features, making them vulnerable to breaches and ransomware attacks.
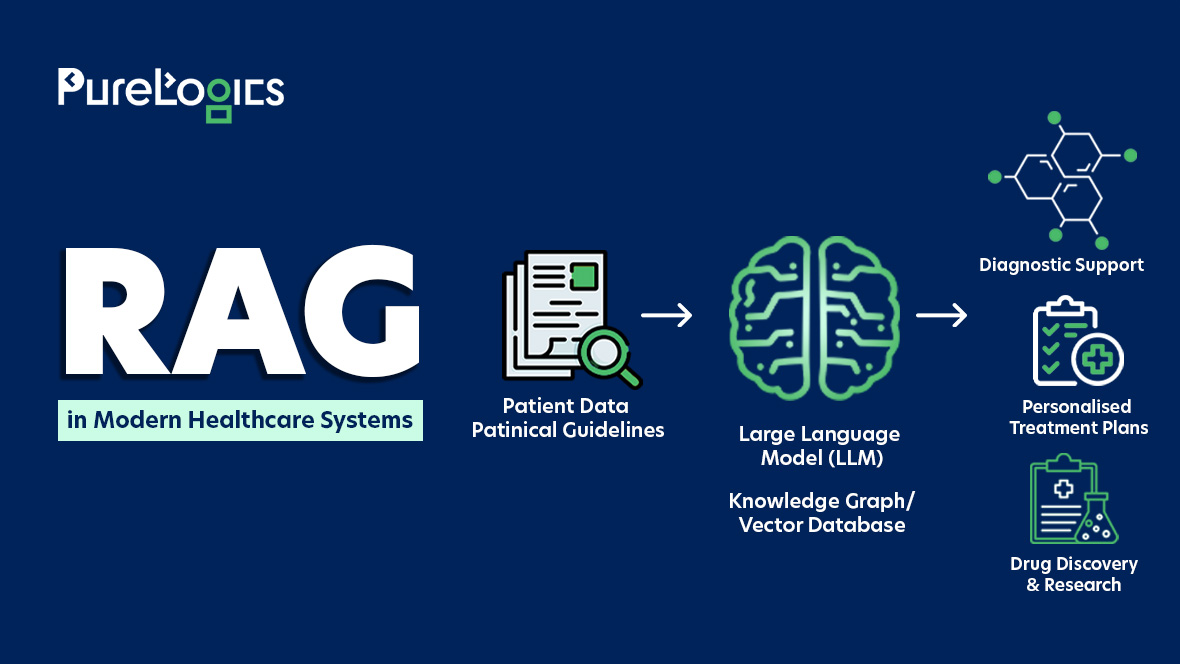
Additionally, with the increasing use of AI in healthcare to enhance patient care and health management, particularly through diagnostics and predictive analytics, the need to secure sensitive data flows has become even greater. Luckily, we have advanced security methods to protect the healthcare applications, and one robust method is E2EE or end-to-end encryption. Let us tell you more about it and why it matters.

What Is End-to-End Encryption and Why Does It Matter in Healthcare?
End-to-end encryption (E2EE) is a security method where the data is encrypted on the sender’s device and can only be decrypted on the recipient’s device. In E2EE, no intermediary can access unencrypted information, including servers, internet service providers, or even application providers.
This is highly useful in healthcare, as patient medical records, diagnostic images, prescription data, and communication between healthcare providers remain completely private and secure, in contrast to traditional encryption methods, which may temporarily decrypt data on servers for storage or processing. At Purelogics, we follow the latest security standards and practices for HIPAA-compliant application development. Let us give you an example of one of our projects Caring on Demand.
It is a HIPAA-compliant caregiver app for iOS, helping certified care providers to connect with nearby care recipients and earn income via the platform. Our team also developed a web-based application that enables patients to schedule and request care services for a particular date and time. With nearly 19+ years of experience, we have created healthcare solutions that include security features such as:
- Multi-Factor Authentication (MFA)
- Access controls and role-based permissions
- End-to-End Encryption (E2EE)
- Audit Logging
We have developed 50+ healthcare projects. Contact us to book a consultation with our healthcare software developers or view our other projects.
In our experience, ensuring compliance becomes difficult for healthcare professionals. Below is the seven-step process that can help in the development of secure healthcare applications.
E2EE Healthcare Application Development Process
Let us walk you through the process of E2EE healthcare application development.
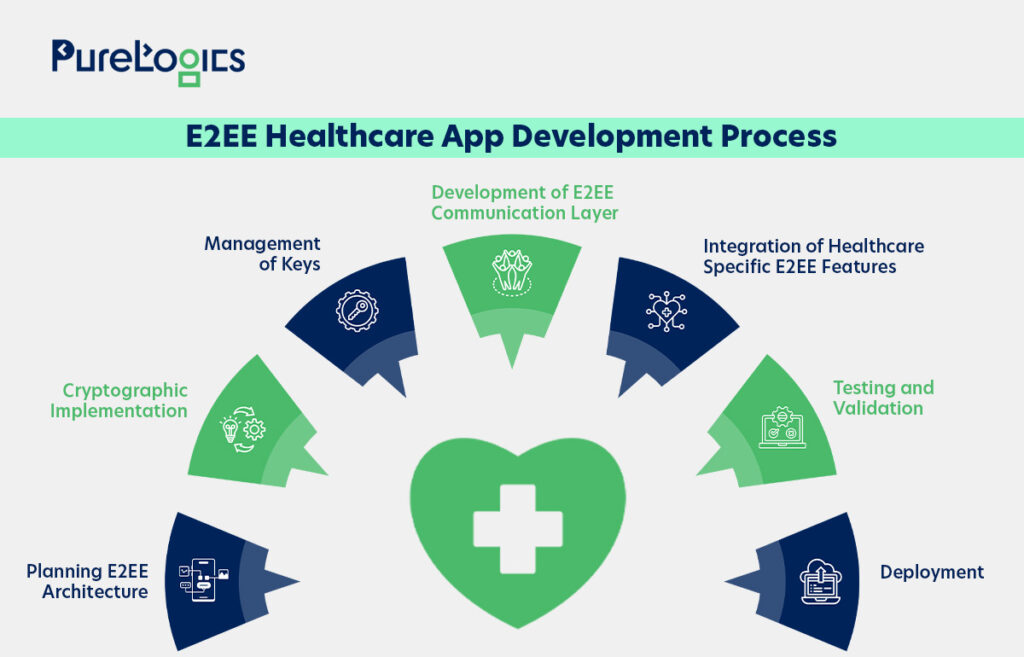
E2EE Architecture Planning
E2E encryption generates two sets of cryptographic keys, one public and one private, for each user using asymmetric cryptography. Here, the zero-knowledge design is employed, ensuring that the data remains encrypted while maintaining the confidentiality required by HIPAA regulations to protect the patient’s health data. Moreover, the client-side encryption/decryption is planned only.
Cryptographic Implementation
The encryption is implemented on both the device and client sides. In device-level encryption, the end-to-end encryption encrypts the data at the source and decrypts it only at the destination, ensuring the data is secure at every stage of the transfer. At the client side, the data is encrypted on the sender’s system or device, and only the recipient can decrypt it. Furthermore, asymmetric encryption protocols are implemented, and unique key pairs are generated per user or device.
Management of Keys
In this step, cryptographic keys are locally generated on user devices and securely exchanged between authorized parties. Furthermore, the implementation of periodic key rotation protocols is fixed.
E2EE Communication Layer
Here, all patient data is encrypted before transmission, and secure channels are established. Furthermore, for the protection of metadata, the metadata exposure is minimized during transmission. Additionally, the sender and receiver identification are verified.
Healthcare-Specific E2EE Features
Some of the specific security features, such as multi-party access, are implemented in addition to the establishment of emergency access protocols, creation of encrypted audit logs for compliance, and secure data transfer mechanisms between healthcare entities. In this phase, developers also ensure that security is balanced with app performance.
Testing & Validation
In this step of the process, the encryption and decryption functionality is tested across all devices. Additionally, a few other things that are tested are given below:
- Testing of emergency access and exchange procedures.
- The app’s performance is tested under an encryption load.
- Testers verify that no server-side decryption capabilities exist.
- Validate key exchange mechanisms.
Deployment
Here, a gradual rollout is preferred, meaning E2EE is deployed incrementally, and healthcare staff are trained on E2EE workflows. Additionally, regular monitoring is conducted to safeguard sensitive patient data.
Ongoing Maintenance
The maintenance of the E2EE healthcare applications requires continuous cryptographic updates to address the vulnerabilities. Furthermore, maintenance ensures ongoing adherence to HIPAA and HITECH regulations through regular audits and detailed logging of all security activities.
The main difference between E2EE is that no intermediate party, including the servers, can decrypt the data. Only the recipient, meaning the intended healthcare provider and patient devices, has access to the unencrypted information.
To implement this level of security while maintaining performance, several technical best practices must be followed.
Technical Best Practices for Building Scalable Encrypted Healthcare Applications
Healthcare solutions architecture is complex because of the transmission of data. A delicate balance is required between security, performance, and compliance. Our healthcare software development team, with nearly 19 years of experience, ensures that patient data remains protected by following proven technical best practices. Therefore, delivering reliable and high-performing digital healthcare experiences.
Zero-Knowledge Architecture
The implementation of zero-knowledge architecture ensures that servers never have access to unencrypted patient data. Furthermore, the systems are designed so that encryption and decryption occur only on client devices, with the backend routing and storing encrypted payloads. So if the servers get compromised, the patient data remains protected. Additionally, design your database schema to separate encrypted medical data from metadata, and perform key derivation on the client’s side using algorithms (PBKDF2 or Argon2).
Management and Distribution
Design a robust key management system that strikes a balance between security and usability. Make sure to develop encryption keys for each patient based on their credentials, with additional layer keys for situations where shared access is involved (patient-doctor consultations). For real-time communications, use secure key exchange protocols such as the Signal Protocol or Double Ratchet. You can also consider implementing key escrow mechanisms for emergency access whilst maintaining the end-to-end encryption principles. Additionally, store secure keys using hardware security modules (HSMs) or other storage solutions such as Trusted Platform Modules (TPMs), and implement strict key rotation policies.
HIPAA-Compliant Application Development
The Health Insurance Portability and Accountability Act, or HIPAA, mandates the secure transmission and storage of data. Non-compliance can lead to heavy fines; therefore, the infrastructure of healthcare applications should be designed to meet HIPAA requirements while maintaining E2EE capabilities. The few steps you can take in this regard are:
- Ensure that the encrypted data itself is never recorded.
- Implementation of audit logging to track all data access activities.
- Ensure your cloud infrastructure features strong and proper network segmentation.
- Schedule routine security evaluations.
- Make sure that data retention and deletion policies are properly defined.
Performance Optimization
Optimize your encryption implementation to efficiently handle large medical files like video consultations and imaging data. Make sure to use streaming encryption for handling large files and use efficient compression algorithms before encryption. You can also explore progressive encryption methods for real-time data streams. Furthermore, use modern cryptographic libraries that support hardware acceleration and implement caching mechanisms/strategies that work with encrypted data to minimize processing load.
Securing Client Side
Strengthen the client applications to resist the threats and common attacks that could compromise encryption. Also, manage user sessions securely with features like automatic timeouts and ensure the sensitive data is stored using secure mobile storage systems (Android Keystore or iOS Keychain).
Pro Tip: Create authentication processes that never expose encryption keys during data access or login.
Scalable & Adaptive Cryptographic Protocols
Select the cryptographic protocols that grow with your user base while maintaining powerful security standards. Implement efficient group encryption methods for multi-party or collaborative medical consultations. Furthermore, use resource-efficient protocols for connected medical devices and develop your encryption framework to support forward secrecy.
Add Real-Time Communication Features
Develop secure real-time communication features for medical collaborations and telemedicine consultations. Furthermore, use protocols like SRTP for end-to-end encrypted video calling and design a secure instant messaging system with perfect secrecy, and ensure that file sharing maintains encryption (during data transfer or storage). Optimize for low latency without compromising security, and implement proper error handling to prevent details about encrypted messages from being revealed.
Monitoring & Auditing
Establish a thorough monitoring system that tracks security metrics while preserving privacy integrity. Furthermore, make sure to implement automated compliance checking that verifies the encryption status, monitors and detects unusual access patterns, and ensures adherence to security protocols. Additionally, create audit trails that satisfy the regulatory requirements while upholding the zero-knowledge architecture and establish clear alert systems for potential security incidents that can respond without accessing encrypted data.
Disaster Recovery
Create disaster recovery procedures that support encrypted data and use secure backup solutions that maintain encryption during backup and restoration. Additionally, define protocols for restoring encrypted keys in emergencies and account for scenarios where encryption keys may be compromised.
Pro Tip: Do regular testing of your recovery procedures and maintain offline backups of critical system components while maintaining security.
Integration of Security Patterns
Develop and establish secure integration practices to connect with other healthcare systems while maintaining end-to-end encryption. Furthermore, implement secure API gateways that can route encrypted data without decryption, and develop and design integration protocols that support patient privacy across different boundaries. Additionally, utilize standardized healthcare data formats, such as FHIR, with enhanced encryption layers.
These best security practices should be the foundation of developing healthcare applications that safeguard patient privacy through end-to-end encryption, in addition to meeting the scalability and compliance requirements of modern healthcare systems.
Key Challenges in Developing Encrypted Healthcare Applications
Healthcare solutions are complex, and ensuring their security is a big task, keeping in view the constant transmission and storage of data across different devices. Below are some of the challenges you can encounter:
- Complexity in Key Management: The secure storage and rotation of encryption keys can be a challenge.
- Performance Overload: Maintaining a strict balance between encryption strength and application speed, especially for real-time data, can be tough.
- Implementation: Ensuring data remains encrypted during transmission and at rest, including third-party integrations, can be difficult to get right.
- Data Access Control: Logging and restricting access to encrypted data for different user roles can be time-consuming and tricky.
- Interoperability Challenges: Maintaining encryption compatibility across systems, such as EHRs, cloud storage, and APIs, can be cumbersome.
- Telehealth and Mobile Integration: It can be challenging to encrypt data on mobile devices during virtual care sessions without compromising the UX.
- Data Recovery: Ensuring that encrypted backups can be successfully restored without compromising security standards or compliance requirements.
Conclusion
Developing a secure, end-to-end encrypted healthcare application is not just about checking the compliance boxes. It’s about protecting the sensitive details about people’s lives. If you are facing security challenges, don’t take them lightly, because when someone trusts your healthcare solution with their medical history, they are placing their confidence in your ability to keep that information safe. At Purelogics, security is our utmost priority, driving us to develop solutions that can save you from potential breaches. We are a trusted name in the industry! So book your consultation with us.

FAQs
What is the use of encryption in healthcare?
Encryption in healthcare involves converting sensitive patient data into coded language, allowing it to be accessed only by authorized individuals. This helps protect medical records, prescription details, diagnostic images, and personal health information.
How to implement encryption in healthcare?
To implement end-to-end encryption in healthcare, first encrypt the data on the sender’s device before transfer and only decrypt it on the recipient device (using private keys). You can also use strong encryption protocols such as AES-256, etc.
What is the protocol for end-to-end encryption in healthcare?
The protocol for end-to-end encryption in healthcare involves using standards such as TLS 1.3 for secure data transmission and AES-256 for encrypting sensitive health information.


 [tta_listen_btn]
[tta_listen_btn]
 July 28 2025
July 28 2025